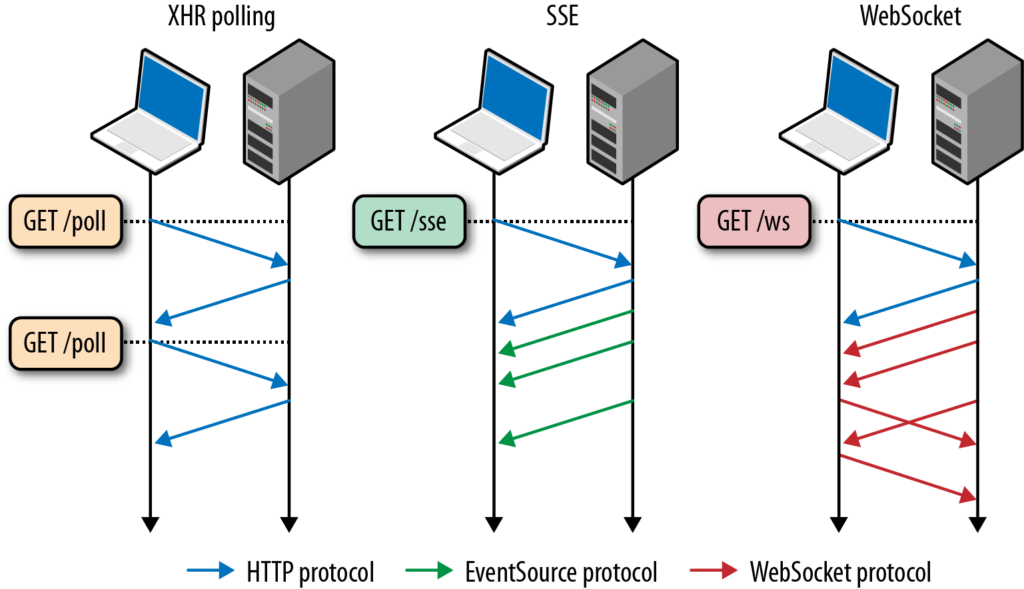
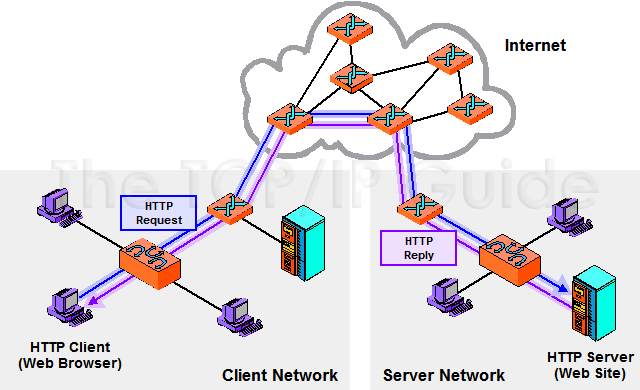
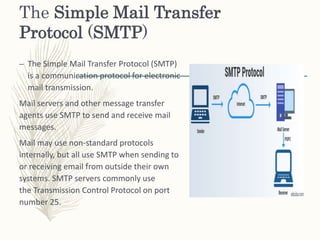
![PDF] Native Web Communication Protocols and Their Effects on the Performance of Web Services and Systems | Semantic Scholar PDF] Native Web Communication Protocols and Their Effects on the Performance of Web Services and Systems | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/36d575cb0bc7eab915a676b914cf4f79f6a63c88/3-Figure3-1.png)
PDF] Native Web Communication Protocols and Their Effects on the Performance of Web Services and Systems | Semantic Scholar

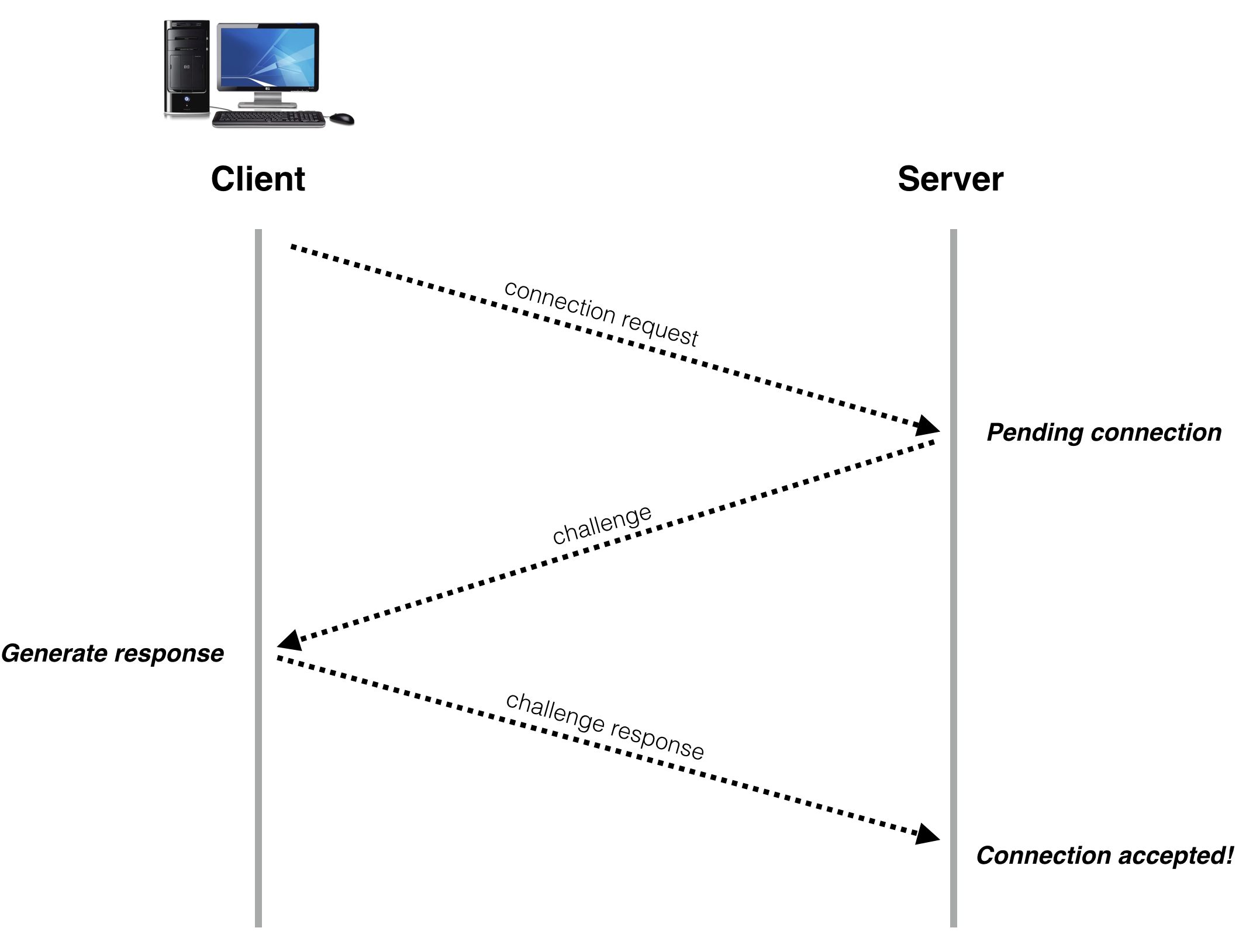
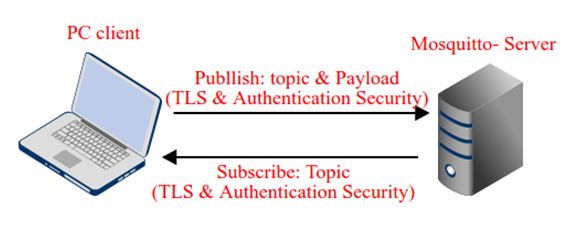
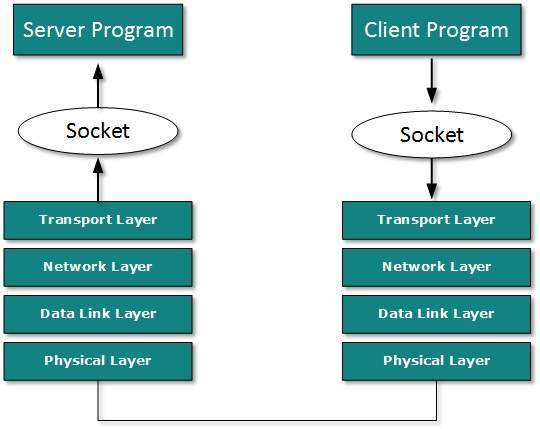
System and method for designing secure client-server communication protocols based on certificateless public key infrastructure - diagram, schematic, and image 02

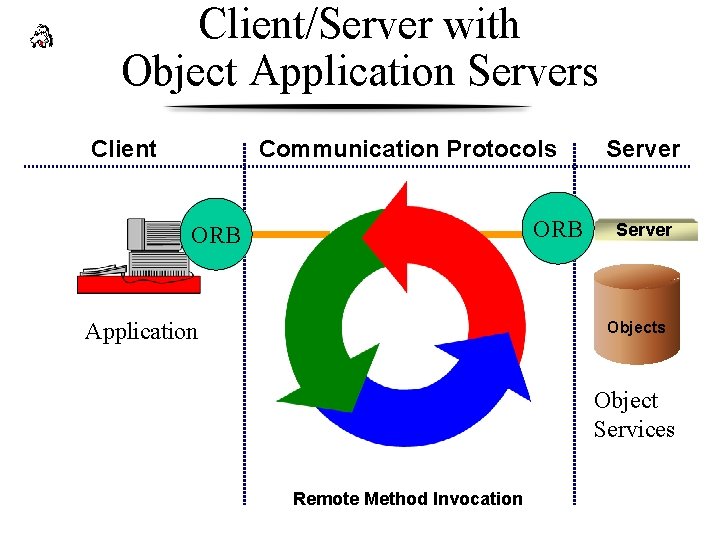
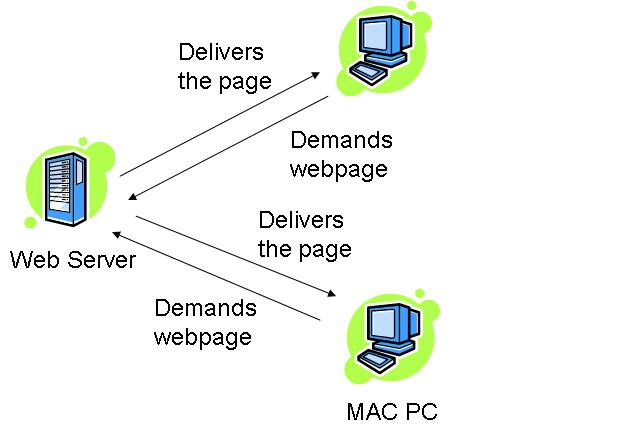
Wi-fi Communication protocol: a.) Client -Patient #, b.) Server and c.)... | Download Scientific Diagram